Visiting Cyber Security Nordic event in Helsinki Expo and Convention Centre
Today I was visiting at the ”Cyber Security Nordic” -event and got to see a lot of booths from different companies providing their security solutions.
Here’s some I found interesting.
Bittium
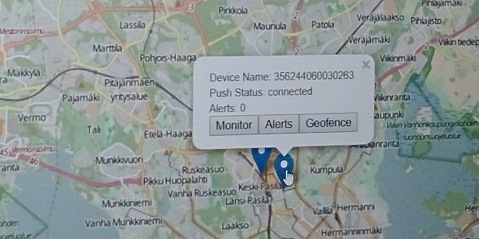
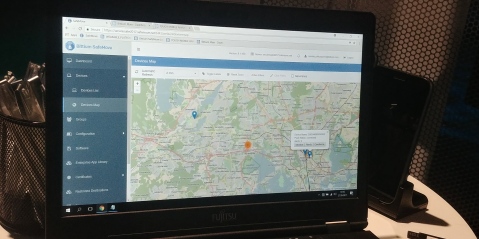
Bittium does a several kinds of industrial security products and services. For this event, they were introducing Bittium Secure Suite -software and Bittium Tough Mobile C – mobile phone. The promoter said that they provide the suite as a standalone service for companies’ internal server systems, so the phones can use the server as VPN-gateway with two-way communication, so the administrators can keep on track of the phones and remotely control the phones, if needed, eg. lock the phone, turn it off, boot it up.

The Bittium Tough Mobile C is, according to the promoter, hardware manufactered in Finland and the OS is self-developed port from the Android (full phone specifications can be found here https://www.bittium.com/bittiumtoughmobile). The mobile OS has Finnish national security level 3 certification from NCSA-FI . According to this announcement from the national security centre , it’s currently the only mobile phone system in finnish market, that has such a certificate. Of course this matters only in Finland, but still it seems promising on era of business secret leaks and advanced security breaches. Maybe later they are going to chase for EU-level certificate to ensure sales in global level. The certificate only proves, that there won’t be much competitors on the same level in Finland, but in international level, there might be other companies with their own solutions, like Blackphone is currently providing for consumers.
Their suite has also been certified by NCSA-FI, which has a several requirements, like development has to be done in a radiation isolated room. It also means that there won’t be any similiar product, that could be developed on open communities and have the software certified in a same way as the Bittium Secure Suite.
On the other hand, they indeed rely on open source products by using android as a base of their Secure OS (stripped from the google services, as the promoter said) and their suite runs on top of centos/RHEL.
As a competitors, the promoter mentioned that they have several of them especially focusing on consumer market, when they are relying more on b2b-customers and consultancy on initialization of the product suite.
Jetico
At Jetico-booth, the promoter mentioned they had their BestCrypt product available before Truecrypt and, according to wikipedia, it really has been around since 1995. On a competitor level, there’s of course free software available from ruins of the old TrueCrypt: VeraCrypt. On comparison, Veracrypt supports more algorhitms, but BestCrypt seems to have RAID and UEFI -support and a good compatiblity with Windows boot sector encryption, few to mention.
On their website, they try to gain attention of former Truecrypt users to move to the Bestcrypt. Especially it’s visible on their website, where they have stories from the truecrypt-users about switching to the BestCrypt http://www.jetico.com/solutions/by-need/wiping/40-case-study/use-case/455-why-is-bestcrypt-the-best-truecrypt-alternative-users-tell-why. It’s naturally obvious that they have picked the most positive reviews among others. They seem to even have their own comparison chart on BestCrypt vs TrueCrypt.
The comparison chart shows, that there’s some extra features available on BestCrypt, that TrueCrypt/VeraCrypt doesn’t provide. On the other hand, you can use BestCrypt binaries with 21 day free trial and to continue, you need to buy either of the licenses: BestCrypt Container (for encrypting files and folders) 59.95€/year and BestCrypt Volume (for encrypting whole partitions) 99.50€/year. If you need to encrypt your remote computers, you need to buy enterprise license for central management software, which requires to ask an offer from their consultant.
When you keep in mind, that Veracrypt can do both hidden volume encryption and encrypt whole partitions and, at the same time, provides all this under free software license, it’s pretty obvious which software a regular user (especially old truecrypt users) would favor.
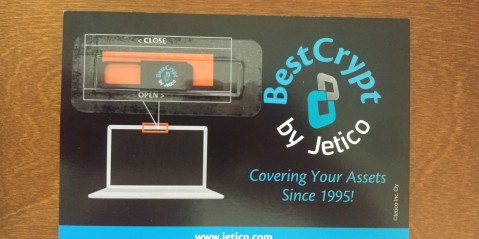
To spice up their event booth, they had these really cool slide cover for your laptop’s webcam, which definitely is better than plain tape, if you need to participate in video conferences.
Dimecc
Dimecc is not an actual company, instead it’s a coalition, or ecosystem as they refer on their web page, helping the private sector and the university researchers to come closer together in national and global level. There’s several means to do this, like let companies to vote, what research teams would focus in Dimecc’s partner universities.
The funding comes mostly as project-based from the funding agencies and private company proposals, so the funding is mostly result-based and can be focused on original research or political lobbying.